Canadian Program for Cyber Security Certification (CPCSC): Evaluation Findings Explained
What can the evaluation tell us about the initial roll out of the CPCSC?
Canadian Cyber in Context is sponsored by
All views expressed belong to Canadian Cyber in Context and do not reflect the position of any sponsor.
Feature your business in Canadian Cyber in Context through sponsorship.
In 2025, Public Services and Procurement Canada (PSPC) conducted an evaluation of the Canadian Program for Cyber Security Certification (CPCSC). Luckily for us, the full report and management action plan were released to the public early this year.
The evaluation covered the period from April 2023 to June 2025, which includes the soft launch in early 2025. This means this only covers the initial preparation and phase 1 of implementation for CPCSC, and roughly a year of CPCSC activity is not covered by this report. Despite this gap, we get some interesting insights into program’s organization and the delays that occurred during this time. In particular, the report confirms much of what has been unspoken about CPCSC and the program's direction since January 2025.
Although this evaluation focuses on a period approximately a year ago, note that it was conducted specifically to improve the program, and a management action plan was developed in response. As a result, we can use the report and the management action plan to understand the CPCSC's current operations and direction.
With that said, the CPCSC Secretariat officially released CPCSC level 1, including the level 1 self-assessment tool and scoping guide. As much as this evaluation can inform us about the program itself and how it is developing, the program itself is continuing and making progress. Despite this major progress and milestones, the program still needs ongoing industry and stakeholder feedback on its activities, as this evaluation found.
Andrew Laliberte and I are underway with reviewing the new materials and hope to have a lot more out soon about CPCSC level 1, so make sure you are subscribed.
What is the Evaluation?
PSPC’s Departmental Evaluation Plan for 2024-2025 to 2026-2030 included a mandatory evaluation of CPCSC, which was conducted by the Evaluation Services Directorate between April and June 2025. The evaluation focused on “assessing stakeholder engagement and its contribution to CPSCC implementation, the extent to which risk management practices have been employed, as well as the prioritization of activities and available resources.” To assess these variables, the evaluators reviewed documents, conducted interviews and surveys.
As noted, the evaluation was conducted to improve the program, in particular, to ensure that the CPCSC program, as it is being rolled out, is in line with the priorities of the Government of Canada, to assess PSPC’s support of the program, and the inclusion/role of other departments in the implementation of the CPCSC.
In response to the report, PSPC developed a Management Action Plan, which will be reviewed at the end of this article.
Key Findings
The key findings of the evaluation are divided into three categories: relevance, effectiveness, and delivery.
Issue 1: Relevance
Relevance generally asks,” Why do we even need the CPCSC?” The answer is simple: Canada needs a mechanism to ensure the security of sensitive government data in non-government systems. CPCSC has been developed to fill this gap.
Although reciprocity with the United States’ Cybersecurity Maturity Model Certification (CMMC) was one of the primary motivations for creating the CPCSC, the CPCSC remains relevant and necessary regardless of alignment with other programs. Nevertheless, as will be discussed more later, the lack of reciprocation with CMMC had a major impact on the program.
One key question that was asked, and continues to be asked, is why CPCSC was not integrated into PSPC’s existing programs, such as Contract Security Program (CSP) and Controlled Goods Program (CGP). The report explains that CPCSC, CSP, and CGP all require specific compliance and assurances that, while complementary, address different areas that are governed by different policies and authorities. In particular, CSP is managed under the Policy on Government Security and CGP is governed by the Defence Production Act and Controlled Goods Regulations. CPCSC is managed under the Policy on Government Security and is defined by the ITSP 10.171 and ITSP 10.172 standards (10.172 not yet released).
Issue 2: Effectiveness
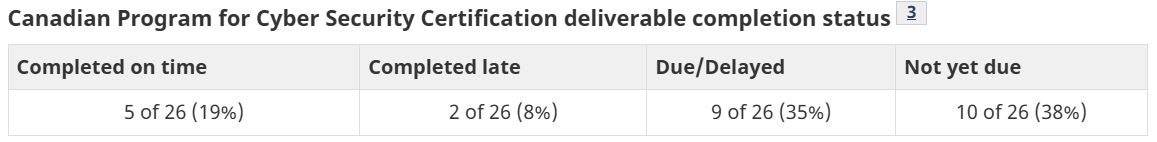
As CPCSC is still an in development program, effectiveness predominantly deals with the program’s ability to deliver the program based on its own timeline and goals. Unfortunately, the report obfuscates the actual effectiveness of the program delivery by putting it into the context of the entire program versus the completion status of deliverables during the period examined. As a result
The report explicitly states that the CPCSC implementation was slower than anticipated due to “factors such as the need to redevelop it with a Canada-only focus in early 2025.” In other words, Canada did not anticipate the United States' refusal to agree to reciprocity and thus had to switch to a Canada-only approach. What I find curious is that the phrasing makes it sound like there was a completely different plan and design for the program, and that they had to make modifications to launch it in March 2025 rather than January 2025. This begs the question as to what was so different to require changes, or was this a reassessment of the overall plan about CPCSC. Despite this lack of reciprocation, CPCSC is still based on CMMC and the ITSP 10.171 standard that is used in CPCSC is based on CMMC’s NIST 800-171. Further, the recently released self-assessement tool is based heavily on United States tools and wording. So there appears to be very little change.
Although the report states the delays are a result of a lack of reciprocity, a more kind interpretation would likely be that, after the initial delay, the delays have had a domino effect. These delays have been compounded by additional, more recent delays in CPCSC implementation that were not covered in the evaluation. All of this is understandable, and perhaps their timeline was optimistic in the first place, but what has increasingly frustrated industry and stakeholders is the CPCSC secretariat's lack of communication, which quietly updates its website with new dates and timelines.
While the program ultimately continues to roll out with occasional delays, the lack of communication about these delays and the resulting frustration are not captured by this report. However, as will be shown, we at least have an answer for this lack of communication.
Feature your business in Canadian Cyber in Context through sponsorship.
Issue 3: Delivery
Issue 3 predominantly deals with the governance and overall organization of CPCSC program and its secretariat to implement the program. In other words, less to do with the work of implementing the CPCSC and more to do with the work of the government implementing the CPCSC program. Overall, the CPCSC secretariat reported satisfaction with PSPC's support, but there was a need to clarify roles and responsibilities in administering the CPCSC.
Despite this, the report greatly overstates the organization and governance of the CPCSC and makes it sound like they have more resources and support than they have. The report states that the CPCSC is supported by clearly defined governance that includes The ADM Cyber Security Commtitee, Director General committees, and the Tiger Team. The Tiger Team Working Group is the group actually responsible for developing and implementing the CPCSC. So while the ADM Cyber Security Committee and Director Generals do technically have oversight and manages the Tiger Team, this is like saying Cabinet oversaw the creation of the Defence Industrial Strategy. While technically correct, the actual writing and work is done by a smaller team that reports up.
The precise composition of the The Tiger Team Working Group, also known as the CPCSC Secretariat, is unclear, but it is primarily composed of and led by members of PSPC’s Defence and Marine Procurement Branch and the Departmental Oversight Branch as the designers, implementers, and technical authority for the CPCSC. They are then supported by an inter-departmental group from DND, Treasury Board Secretariat, Communications Security Establishment/Canadian Centre for Cyber Security. The Standards Council of Canada is mentioned among partners, but as a Crown corporation, it is likely more of a partner than an active participant on the Tiger Team. This small, multi-departmental team is what has allowed them to stand up the program without running into mandate issues and ensure everyone is involved without being enormously slow.
One of the biggest complaints I have heard related to CPCSC thus far is about understanding its role in broader government cybersecurity compliance, such as the role of Canadian cloud profiles and CPCSC/ITSP 10.171. The reason that there has yet to be any adequate reconcilitation is stated plainly in the report:
“Several interviewees recognized the CSE-CCCS as the primary source of cybersecurity technical expertise for CPCSC and noted their limited involvement to date, citing a lack of funding and capacity as a barrier.”
CPCSC essentially rely upon CSE/CCCS for technical expertise related to the standard, but their capacity to deal with anything other than the standard are significantly limited or non-existent. As much as the Tiger Team organization has allowed them significant leeway to develop the CPCSC, there are limitations as it relates to the implementation of the program. The report notes insufficient technical cybersecurity expertise within CPCSC stakeholder departments, leading to reliance on technical authorities and experts such as CSE/CCCS.
These existing gaps were identified as risks to the ongoing implementation of CPCSC and could lead to further delays in the program.
This is closely related to the CPCSC's risk management. The report notes that the Secretariat undertook significant efforts to identify risks and included multiple stakeholders in this process, but there was minimal activity to address the identified risks, other than to help inform the planning and implementation of the CPCSC. Despite this, some interviewed noted that some risks were not fully addressed, which include:
SMEs are struggling with the financial and technical demands of CPCSC
Lack of reciprocity
Insufficient personnel, project management, and technical cybersecurity expertise in CPCSC stakeholder departments
Inconsistent stakeholder priorities, coordination, and engagement
Unclear plans to transfer CPCSC management following implementation.
Take note that all of these risks have still not been adequately addressed. While some issues may not be fully addressable, such as the lack of reciprocity, CPCSC has found a middle ground by allowing CMMC to apply to CPCSC on a case-by-case basis.
The management action plan includes details related to the development of CPCSC risk management tools after the evaluation was completed, but these tools do not neccesarily address the full breadth of risks noted above.
Long Term Program Governance and the CPCSC
What CPCSC is and where to start have already been covered in detail, but this report does a good job of showing how many different departments and teams are involved. Here is a breakdown of the overall structure of those involved, including those outside of the program (Thanks to Andrew Laliberte):
DM Committees (Defence Procurement Strategy)
└── ADM Committees (GC Cyber Security Oversight)
└── DG Cyber Security Certification Steering Committee
└── PSPC – DMPB (Program Lead)
└── CPCSC Secretariat
├── DOB (Technical Authority / Business Owner)
├── Procurement Branch (Data Systems)
├── Tiger Team Working Group
│ ├── PSPC (DMPB + DOB)
│ ├── DND (Client / Assessments)
│ ├── TBS (Policy)
│ ├── CSE / CCCS (Technical Authority)
│ └── SCC (Accreditation)
└── External Ecosystem
├── Industry (Suppliers)
├── Third-Party Assessors
└── Cyber / IT ProvidersBefore CPCSC and informed folk yell at me, I know this does not fully/accurately reflect how the Tiger Team is organized, but it is a rough breakdown of the overall organization and stakeholders involved. it is meant to show just how many people are involved in this. As much as we would like to complain about a lack of communication or about how CPCSC is developing or being delayed, they’re essentially doing a giant juggling act among the different mandates of the organizations involved in this process.
The report is very explicit that a lack of personnel, project management, and cybersecurity knowledge is affecting implementation. The Tiger Team organization gives them a lot of flexibility, but may not have the capacity to accomplish everything to ensure that the program’s successful implementation. This should be a major concern for the government, military, and defence industry, as this is essentially saying CPCSC does not have the resources it needs.
Costs
One particular passage really stood out to me that I want to unpack:
“The evaluation also found that cost to industry is a major concern for all cyber security programs reviewed. In the case of Canada, CPCSC Secretariat-led industry engagements in May 2024, reported 46% of sub-contractors expecting to invest less than $50,000, while 29% of consultants projected costs of $150,000 to 175,000. 68% of respondents want comprehensive support: financial assistance, guidance, and resources in order to prepare for CPCSC assessment.”
When PSPC conducted the evaluation, this data was already approximately a year old. At this point, it is one month shy of being two years old and is likely inaccurate.
This data is from May 2024, long before ITSP 10.171 was released. Although we generally knew it would be based on CMMC’s NIST SP 800-171A, CPCSC remains a different mechanism and had to pivot after failing to acquire reciprocity with the United States’ CMMC. As a result, PSPC/CSPSC Secretariat must consider doing another RFI to determine how well industry is beginning to understand CPCSC, especially as level 1 is being introduced.
Takeaways - What Does This Tell Us About CPCSC?
The government has not provided CPCSC with sufficient resources to develop and implement the program.
The program states that there is “insufficient personnel, project management and technical cyber security expertise within CPCSC stakeholder departments.” It is unclear if this has been resolved since this report was released
Part of the problem with this appears to be the level of funding allocated to departments, where DND, the Treasury Board Secretariat, and CSE/CCCS were not given any funding for CPCSC activities despite having a role in implementation.
The need to prioritize funding is also likely what has led to a lack of communication between CPCSC and industry and external stakeholders, as they’re prioritizing program development over engagement. This is a completely understandable approach, but it is making it harder for the CPCSC Secretariat to develop the program.
Communication and engagement with external stakeholders are critical to maintaining an active dialogue for additional feedback and ensuring successful implementation. Ultimately, it is industry that will be implementing the program and be affected by it, so any supply chain program should include the feedback of the supply chain. Deprioritizing engagement due to a lack of funding ultimately hurts the CPCSC and makes their job so much harder.
In the end, the report even confirms this when it states “it was suggested that industry engagement should be increased to boost CPCSC awareness and buy-in, however interviews noted that CPCSC was not provided funds for industry engagement or program promotion.”
The CPCSC Secretariat does not have an accurate survey of the state of the defence industry and CPCSC implementation, particularly costs.
When CPCSC first conducted their RFI a few years ago, CPCSC was still in its very early stages and only 91 organizations responded. There is likely a strong chance that you only responded to this RFI if you were already aware of CMMC and the role it plays on CPCSC.
This is to say that many more organizations are now aware of CPCSC; we have the standard and understand its full scope, so now is a time for CPCSC to release another RFI to gain a better understanding of the preparedness of Canada’s defence industry supply chain and perceptions of CPCSC.
The report specifically notes recognition of the risk of SMEs struggling with financial and technical demands. More information about these risks and concerns from a new RFI and surveys could potentially help persuade the government, that is very defence conscious, to provide additional funding to ensure the success of the CPCSC.
The report specifically highlights the high costs associated with similar compliance programs, especially for SMEs, and notes that Australia used loans and regional development funds. This does not mean that the government will institute such programs, but awareness of this and the compliance costs are a positive step towards the government developing programs to assist SMEs and the broader sector in ensuring compliance. This is optimistic thinking, but these types of evaluations and audits are bureaucratic processes that motivate a lot of action on cyber-related programs in the Canadian government.
The CPCSC Secretariat is temporary
Unless this has changed, the handoff plan seems risky. The evaluation states that “the current CPCSC management model… was designed to be temporary with a reassessment and transfer of management to another entity following program implementation.” Authority and oversight of CPCSC was always going to be vested in other authorities when the implementation of CPCSC was completed, but there does not appear to be long-term thinking about governance of this program.
The evaluation in particular notes that CPCSC’s management is concerned about when CPCSC moves from DMPB in PSPC to “another organization.” Although we know that CPCSC level 3 will be largely be overseen and assessed by DND, there remain questions about the long-term management of the overall CPCSC program. As the CPCSC Tiger Team is a multi-departmental group with an organization and mandate that is unique, it is likely difficult to transition this into normal operations and continue on as normal.
Another aspect that the report overlooks is that the loss of expertise about CPCSC is likely to occur if CPCSC management is transferred. The report only emphasizes ensuring proper documentation of roles to enable short and long-term effectiveness, but this may not capture the full institutional knowledge and experience with CPCSC stand up that will be important during the course of implementation.
As a result, it may be better for the program to transition to long-term management sooner rather than later, as the program becomes more complex, the more difficult it may be to transfer management. Despite the stated problems of lack of technical knowledge in PSPC to manage CSPSC, this can be addressed better with a more long-term arrangement with CSE/CCCS.
Conclusion
There are many in the wider cyber defence and compliance space in Canada that does not give enough credit to the work of the CPCSC Secretariat. As this report notes, the CPCSC has simply not been provided with sufficient resources by the federal government and remains constrained in what it can achieve. Despite these constraints, its unique construction and “Tiger Team” approach have enabled the program to accomplish a great deal with a relatively small team.
It is unclear how much PSPC has been able to adjust its processes based on this evaluation report and the subsequent action plan, because the Management Action Plan only addresses the need for risk management tools and improved program documentation. These types of programmatic actions are relatively easy and do not suggest that the government has yet to provide CPCSC with the appropriate resources to ensure its success.
Although this evaluation covers a relatively old time period, it still tell us a lot about how the program is being developed and what has contributed to the delays. Rather than addressing some of the major risks the program has identified, PSPC has strengthened programmatic functions, since addressing anything beyond this would likely require ministerial or cabinet input.
In the coming weeks, Canadian Cyber in Context will be releasing content and informational content about CPCSC level 1 with Andrew Laliberte. Already, Andy and I are finding that many of the risks identified in this evaluation are affecting the level 1 implementation.