Canadian Cyber News Rewire - 7/03/26
Wiring you into the cyber news relevant to Canada the week ending March 7
The Weekly New Rewire is a survey of cyber or adjacent news stories that I read this past week (or recently). Please leave a comment if you think I missed anything.
Editor Notes:
I have completed the first rough draft of my dissertation (yay!). I will be entering a major editing phase over the next few weeks, so my availability may fluctuate.
Go sign Tanya Janca’s Secure-Coding Petition! (Article on this coming soon)
Coming tomorrow, the first in Compliance is Cash! https://www.cyberincontext.ca/p/compliance-is-cash-where-to-begin
Canadian News
A few really promising companies are being supported through this.
JetScaleAI secures $5.4 million to keep cloud costs and climate impact down
As compute costs continue to skyrocket amid the AI boom, there will be an increasing demand for the ability to reduce costs and increase efficiency.
From Bill C-26 to C-8: Canada’s cyber law reboot explained
A good explainer on the current Bill C-8 making its way through Parliament.
Ottawa puts $8.5 million behind 40 Atlantic Canadian AI projects
Previously harmless Google API keys now expose Gemini AI data
People are stealing Google API keys to use for Gemini, leading to some very shocking surpising costs.
Prime Minister Carney announces changes in the senior ranks of the public service
Chief Information Officer Dominic Rochon of Canada (TBS Secretariat) is now Deputy Secretary to the Cabinet (National Security and Intelligence). This is a big promotion, so props to Mr. Rochon, whom I have only heard nice things about.
Nothing yet on who the next Chief Information Officer is, which is not a good look.
CCCS Cyber threat bulletin: Iranian Cyber Threat Response to US/Israel strikes, February 2026
Nothing major has surfaced yet, but we’re likely to see some reprisal operations. Iran was among the first to use wiper malware with the Shamoon virus against Saudi Arabia in 2012. They have capabilities
Alberta to spend $40M on software upgrades after surge in cybersecurity incidents
Technical debt remains one of the top sources of vulnerability. $40 million for updating “legacy application” is quite interesting and could mean a few different things. A good amount of it is likely to upgrade to software that is currently being supported. Some of these applications are likely to be software that is no longer supported by the developer. Some cases could also be custom software where updates are needed.
AI-generated CRA tax scams increasing, cybersecurity experts warn
Scams and fraud has particularly been helped by AI.
TikTok won’t protect DMs with end to end encryption, saying it would put users at risk
Claims end to end encryption is “controversial,” which is an absolute load of bullshit. I guarantee you this means they’re scraping data from DMs. Do not use Tik Tok.
This is way worse than I would have expected, but I am honestly not surprised. Privacy breaches are usually treated less severe than cybersecurity breaches. While it may seem obvious, both are not the same, but often treated similarly as it involved the segmentation and protection of data. As David Fraser states in the article: "There seems to be no accountability for non-compliance with these laws and policies"
Internal briefing says Canada’s National Research Council remains exposed to high-risk cyber attacks
National Research Council and any research-based organization should have a priority on cybersecurity, but it seems like they’re jumping from incident to incident.
From Iran to Ukraine, everyone’s trying to hack security cameras
Operational technology cybersecurity - so hot right now. More threat actors are aware of operational technology and its importance, so they’re increasingly trying to target it.
Government of Canada Privacy Breach Class Action – Proposed Settlement
Potential class action for privacy breach of Government of Canada account between March 1, 2020 and December 31, 2020. An Approval Hearing will be held on March 31, 2026, at 9:30 a.m. PST
Halifax Water investigating privacy breach, shuts down online portal
Hard to tell if this is a cybersecurity incident yet based on their messaging.
Canada Cyber Threat Watch
While not all attacks are reported or receive media attention, any notable or open-source cyber attacks on Canadian organizations and any relevant cyber threat intelligence to Canada will be posted here. I only list the Canadian Centre for Cyber Security’s (CCCS) alerts here, not all advisories; follow the full feed here.
New AirSnitch attack bypasses Wi-Fi encryption in homes, offices, and enterprises
A new person in the middle attack that intercepts a target’s downlink traffic.
Threat Actor leveraged a Popular AI security testing platform tool for Attack
APT37 Targets Air-Gapped Networks With Novel Malware Strain
Over the past few years we’ve been increasingly seeing unique methods of attack to jump air-gaps. Usually APTs, I don’t think we’ve seen one from a non-APT.
Google says half of all zero-days it tracked in 2025 targeted buggy enterprise tech
Part of this report says that zero-days were exploited by syware makers (15) more oftenthan government-backed espionage groups (12). This should be a concern for everyone because, believe it or not, spyware firms are less trustworthy than governments.
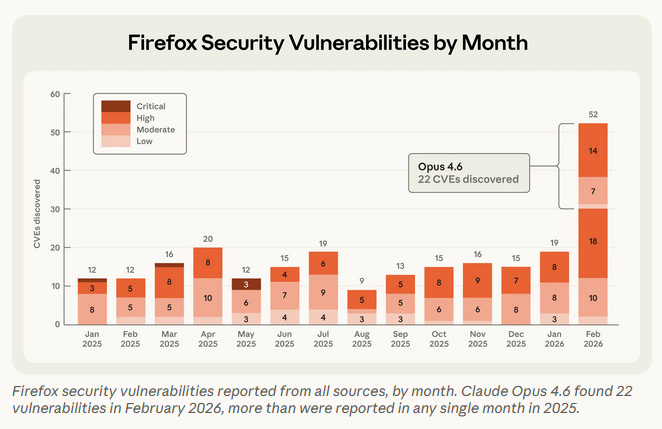
Anthropic Partnering with Mozilla to improve Firefox’s security
Claude is increasingly doing great stuff with vulnerability discovery, so we’ll likely see more and more of these partnerships.
Microsoft: Hackers abusing AI at every stage of cyberattacks
More of what everyone is saying: AI is making it easier for everyone to conduct cyberattacks.
Have your business and logo featured in Canadian Cyber in Context with a sponsorship.
Research and Op-Eds
Read my cyber review of the Defence Industrial Strategy. TL;DR: It will help a lot of Canada’s cyber industry, but there are major gaps and hurdles to overcome regarding infrastructure and hyperscalers.
Cross-Border Data Transfer Regimes: Current Landscape and Outlook Ahead
A good overview at global cross-border data transfer regimes, including Canada.
Link11 Releases European Cyber Report 2026: DDoS Attacks Become a Constant Threat
I feel like we’ve certainly have already accepted DDoS attacks as a constant threat, but few have really elaborated on this.
Fog, Proxies and Uncertainty: Cyber in US-Israeli Operations in Iran
A good overview on the role of cyber in current war against Iran.
United States News
How Cyber Command contributed to Operation Epic Fury against Iran
USCYBERCOM and USSPACECOM were the first to take action, degrading comms and command and control of Iran including its air defence.
Hacktivists claim to have hacked Homeland Security to release ICE contract data
Hacktivist group called “Department of Peace” leaked contract data between DHS Office of Industry Partnership and more than 6,000 companies including Raytheon, Anduril, Palantir, and more.
How OpenAI caved to the Pentagon on AI surveillance
Sam Altman is either lying, is grossly ignorant, or was intentionally misled by the Pentagon. The redlines that Altman thinks the Pentagon agreed to, they actually did not.
CBP Tapped Into the Online Advertising Ecosystem To Track Peoples’ Movements
Every level of United States law enforcement are trying to track your every movement because everyone who isn’t law enforcement is considered a threat to them. Do not travel to the United States unless you have to.
A Possible US Government iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals
I am getting a lot of deja vu about this and the Wannacry ransomware attacks.
The FBI Discusses the Potential to Use AI to Hack Targets
The FBI states this is all hypothetical, but I trust the FBI as much as I trust the Trump administration.
Will NSO’s US Lobbying Pay Off Under Trump?
Those who have bribed Trump with money have achieved significant gains. So, unless there is major internal pushback, then spyware firm NSO will benefit from bribing Trump.
Iran war heralds era of AI-powered bombing quicker than ‘speed of thought’
Anthropic’s Claude and other models used to support the attack on Iran.
Ransomware Breach at University of Hawaii Cancer Center Affects 1.2M People
Ransomware groups love to target healthcare.
How Vulnerable Are Computers to an 80-Year-Old Spy Technique? Congress Wants Answers
United States releases its Cyber Strategy
Six pillars include: Shape adversary behavior; promote common sense regulation; modernize and secure federal government networks; secure critical infrastructure; sustain supriority in critical and emerging technologies, and build talent and capacity.
Long story short: They are out of their depth and it is clear they don’t fully understand what they’re talking about. A lot of hot air. Long story short, they’ll do whatever they can get away with.
FBI investigating ‘suspicious’ cyber activity on system holding sensitive surveillance information
Chinese threat actor access FBI internal network that stores wiretaps and intelligence surveillance warrants.
Some hints that the National Coordination Center may work with private sector orgs for hack-back.
Congress looks to revive critical cyber program for rural electric utilities
Air Force cybersecurity chief tapped to lead Pentagon’s information-security efforts
European Union & United Kingdom News
ShinyHunters Leak 2M Records From Dutch Telecom Odido, Claim 21M Stolen
This will likely continue as Odido has said it will not pay the ransom. I would honestly be a bit worried if I was ShinyHunters. The Dutch have a long history of and are well regarded for their hacking skills, so I wouldn’t be surprised if the Netherlands makes targeting ShinyHunters a priority.
Transport for London hack in 2024 affected around 10 million people, BBC can reveal
BBC claims this is one of the biggest hacks in British history. TfL was attacked by Scattered Spider
Project Compass: first operational results against The Com network
I applaud and celebrate whenever The Com members are arrested.
Major data leak forum dismantled in global action against cybercrime forum
Leakbase forum taken down.
Other International News
North Korea’s APT37 hackers use new malware to breach air-gapped networks
Amazon says drone strikes damaged 3 facilities in UAE and Bahrain
The Iran war has a cyber story. It’s not the one you’re reading
Interplay between Iranian Targeting of IP Cameras and Physical Warfare in the Middle East
Iran appears to be conducting a lot of scanning and using IP cameras to aid in missile target selection.
Israel says it knocked out Iran’s cyber warfare headquarters
Take this with a grain of salt.
Chinese state hackers target South American telcos with new malware toolkit
If you’re a telco, China is targeting you.
She Came Out of the Bathroom Naked, Employee Says
Swedish investigation into the mass privacy infringement of Meta glasses.